Securing Industrial Robots

The use of robots in industrial environments is becoming increasingly common. According to a recent Research and Markets report, the global industrial robotics market accounted for $39.64 billion in 2019 and is expected to reach $101.72 billion by 2027.
“An attacker could exploit them to become persistent within a smart factory, silently alter the quality of products, halt a manufacturing line, or perform some other malicious activity.”
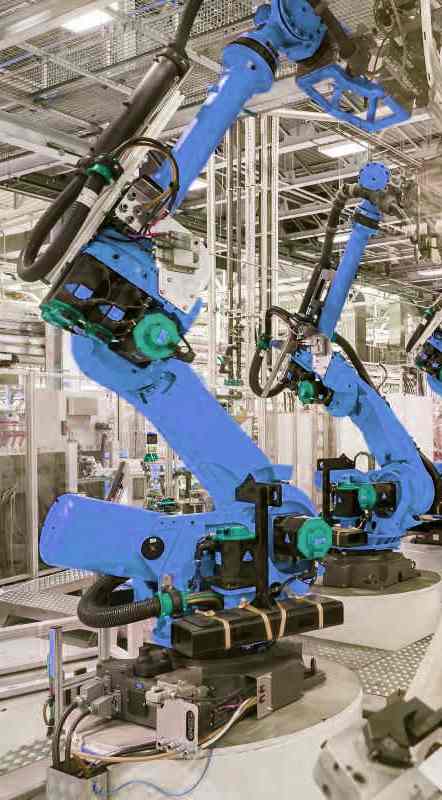
Industrial robots are automated and programmable mechanical systems used for manufacturing. Today, they’re a prominent feature of smart factories. They have a variety of applications and can be used for welding, painting, assembly, disassembly, packaging, labeling, product inspection, testing, and more.
While industrial robots present new opportunities, they also come with challenges. Robots represent yet another kind of endpoint in operational technology infrastructure. And like other innovations introduced to industrial environments in recent years, industrial robots can be exploited by malicious actors.
 In October 2020, a group of researchers from IT security company Trend Micro, Polytechnic University of Milan, and Eurecom Research Institute released a report looking at insecure code patterns in industrial robot programs.
In October 2020, a group of researchers from IT security company Trend Micro, Polytechnic University of Milan, and Eurecom Research Institute released a report looking at insecure code patterns in industrial robot programs.
“Industrial robots are complex and customizable machines that can be programmed with proprietary domain-specific languages,” the report says. “These languages provide not only movement instructions, but also access to low-level system resources such as the network or the file system. Although useful, these features can lead to taint-style vulnerabilities and can be misused to implement malware—on par with general purpose programming languages.”
The recent report was part of ongoing research from Trend Micro and Polytechnic University of Milan around industrial robot vulnerabilities. As far back as 2017, the group of researchers sabotaged an industrial robotic arm as part of a demonstration. The researchers were able to take control of a 220-pound robotic arm capable of wielding gripping claws, welding tools, or even lasers.
“These are industrial weight machines with the potential to cause bodily harm to the humans around them,” Trend Micro exec Mark Nunnikhoven said in a Wired interview at the time.
Earlier last year, the group of researchers put out a report looking at vulnerable and malicious code in industrial programming.
“Since these flaws are difficult to fix, enterprises that deploy vulnerable machines could face serious consequences,” the report says. “An attacker could exploit them to become persistent within a smart factory, silently alter the quality of products, halt a manufacturing line, or perform some other malicious activity.”
The report highlights how design flaws in legacy languages could lead to vulnerable automation programs. According to the report, these insecurities could enable attackers to infiltrate industrial robots to disrupt production lines or steal intellectual property.

Bill Malik, VP of infrastructure strategies for Trend Micro
“Once OT systems are network-connected, applying patches and updates is nearly impossible, which makes secure development upfront absolutely critical,” Bill Malik, vice president of infrastructure strategies for Trend Micro, said in a press release. “Today, the software backbone of industrial automation depends on legacy technologies that too often contain latent vulnerabilities, like Urgent/11 and Ripple20, or varieties of Y2K-like architectural defects. We don’t want to simply point out these challenges, but once again take the lead in securing Industry 4.0 by offering concrete guidance for design, coding, verification, and on-going maintenance, along with tools to scan and block malicious and vulnerable code.”
The “Rogue Automation” report details five attack scenarios, all based on real vulnerabilities found in task programs on public code repositories. These include stealing data, altering a robot’s movements via the network, and using dynamic malware.
“The programming environments for industrial machinery make it easy for attackers to abuse any low-level system resources, because there is no differentiation between privileged and nonprivileged instructions,” the report says. “This is in contrast to the state of almost all modern computing systems.”
The researchers conducted a technical analysis of eight popular legacy programming languages for industrial automation and found that the root cause of the flaws was a combination of powerful primitives that allow unmediated access to low-level system resources.
“Even if the automation technology that drives robots and other programmable industrial machines is completely different from the classic web application running on a Windows server, it could be affected by the very same well-known vulnerability classes (such as path traversal and code injection) and could be targeted by malware,” the report says. “The complete lack of resource isolation (such as a permission system) within the programming and execution environments for control process automation means that there are no stopgap measures that prevent attacks from happening.”
As part of the report, Trend Micro worked with the Robotic Operating System Industrial Consortium to establish recommendations to reduce the exploitability of the identified issues. Among them are guidelines for writing secure task programs. This involves treating industrial machines as computers and task programs as powerful code, authenticating every communication, implementing access control policies, always performing input validation, always performing output sanitization, implementing proper error handling without exposing details, and putting proper configuration and deployment procedures in place.

Christoph Hellmann, Program Manager, ROS-Industrial Consortium Europe
“Most industrial robots are designed for isolated production networks and use legacy programming languages,” Christoph Hellmann, Program Manager, ROS-Industrial Consortium Europe, said in the release. “They can be vulnerable to attacks if connected to, for example, an organization’s IT-network. Therefore, ROS-Industrial and Trend Micro have collaborated to develop guidelines for correct and secure network set-up for controlling industrial robots using ROS.”
In addition to these guidelines, cybersecurity providers have created solutions to better secure industrial robots. In December, Kaspersky and Alias Robotics announced they had partnered to boost cyber-protection for robots used in operational technology infrastructure.
“Robots have their own networks, technologies, safety requirements and business priorities, all of which must be uniquely addressed,” Víctor Mayoral Vilches, CTO and Founder at Alias Robotics, said in a press release. “These systems demand specialized cybersecurity measures that need to happen at the endpoint to guarantee no-human-harm. Our Robot Immune System (RIS) supports more than 40 different robots today and we are partnering with best in class industrial networking monitoring solutions to secure robots in OT environments. By integrating RIS into Kaspersky Industrial CyberSecurity, our clients can now protect their robots with RIS and manage the security of their ICS infrastructure seamlessly via Kaspersky’s solution”
Alias Robotics’ Robot Immune System is a dedicated robot endpoint protection platform. Combined with Kaspersky Industrial CyberSecurity the two protect all levels of the OT environment where robots are used, including robot controllers, processes, and operations. The system was tested with three attack vectors: process network insider, controller insider and compromising the robot operating system (ROS) network.

Anton Shipulin , Solution Business Lead, Kaspersky Industrial CyberSecurity
“As the OT infrastructure becomes more complex, it is important to add security for each of its parts and layers, Anton Shipulin, Solution Business Lead, Kaspersky Industrial CyberSecurity, Kaspersky, said in the release. “Protection measures and tools should also work smoothly with each other to cover the entire environment without any gaps. Considering the growing implementation of industrial robots, this partnership with Alias Robotics allows our customers with robots in their infrastructure to meet the demand for reliable protection.”










