ISA Global Cybersecurity Alliance releases guide to ISA/IEC 62443 standards
ISA Global Cybersecurity Alliance releases guide to ISA/IEC 62443 standards. In 2017, cybersecurity company Kapersky released a report looking at the state of industrial cybersecurity around the globe. The report, produced in part by B2B research company Business Advantage, revealed that the average cost of an attack on an industrial control system was $347,603. For larger companies with more than 500 employees, the average cost was even higher at $497,097.
However, today’s attacks on industrial control systems are costing more than financial resources. Documented attacks on critical infrastructure and manufacturing have resulted in injuries and in some cases even loss of life.
Fast forward to 2019 and Control Systems Cyber Security Association International released the results of a survey of 300 individuals responsible for the cybersecurity of industrial and automation systems. According to the report, roughly 1 percent of respondents admitted that a recent security incident at their organization resulted in injury and 1 percent said the incident led to loss of life.
For decades, the International Society of Automation, formerly known as the Instrumentation, Systems, and Automation Society, has been working to help organizations guard against cybersecurity threats. To this end, in 2019, ISA announced the formation of the ISA Global Cybersecurity Alliance to advance cybersecurity awareness, readiness, and knowledge sharing.
“The ICS cybersecurity threat landscape is becoming more complex, with more direct attacks on control system, IT, and OT infrastructure. Frequently backed by hostile nation-states, malevolent actors are becoming more sophisticated at targeting specific aspects of industrial control systems that have the potential to wreak havoc in the physical world, such as process safety systems,” said Larry O’Brien, Vice President of Research for ARC Advisory Group, a technology research firm, said in a press release announcing the new alliance. “Standards and frameworks are valuable, but end users also need the resources to take the guidance provided by standards and put it into practice in real-world plant and OT environments. ARC applauds this effort to increase the security of industrial facilities.”
Since it’s creation, the ISAGCA has worked to promote the ISA/IEC 62443 series of standards. The ISA/IEC 62443 standards are the world’s only consensus-based cybersecurity standards for automation and control system applications.
At the start of 2020, the alliance committed to producing an easy-to-follow, condensed guide to implementing the ISA/IEC 62443 series of standards as well as a consolidated matrix that cross-references all cybersecurity-related standards to ISA/IEC 62443 principles.
“Unifying and intensifying the work of experts around the world, regardless of affiliation, is a key part of ISAGCA’s mission. We believe that automation providers, cybersecurity vendors, asset owners, government agencies, research groups, and others involved in cybersecurity efforts are stronger together, collaborating to deliver solutions that meet the needs of industry today and tomorrow,” ISA Executive Director Mary Ramsey said in a January 2020 press release. “We are proud to bring together a diverse group of thought leaders to advance the state of cybersecurity.”
To this end, in March of 2020, the alliance released the “Quick Start Guide: An Overview of the ISA/IEC 62443 Series of Standards.” The new guide provides a high-level view of the objectives and benefits of the ISA/IEC 62443 standards and how to navigate them.
Here’s what you need to know about this new guide.
Fundamental Concepts
The first core concept covered in the guide is risk management, which involves the processes and technical requirements that are needed to secure the system, based on risk.
“The methodology used must be established by the Asset Owner and should be consistent with the overall risk assessment methodology of the organization,” the guide says.
This includes risk management which involves the partitioning of a system into smaller zones or a set of assets that share a common set of security requirements.
“A Zone is defined as a grouping of logical or physical assets based upon risk or other criteria such as criticality of assets, operational function, physical or logical location, required access, or responsible organization. A Conduit is defined as a logical grouping of communication channels that share common security requirements connecting two or more zones,” the guide says. “Partitioning the System Under Consideration into Zones and Conduits can also reduce overall risk by limiting the scope of a successful cyber-attack.”
Another core concept is security levels which relates to the level of confidence within an organization that the system under consideration, zone, or conduit is free from vulnerabilities and functions as intended.
There are three types of security levels used throughout the ISA/IEC 62443 standards. These include capability security levels which state that a particular system or component is capable of meeting the SL-T natively without additional compensating countermeasures; target security levels, which are used to select products and additional countermeasures during the integration phase of the IACS lifecycle; and achieved security levels which are the actual levels of security for a particular automation solution and are measured after the solution is commissioned and in operation
The standards also focus on design principles. The first of these is the “Secure by Design” principle which dictates that security measures must be implemented early in the lifecyle of the IACS.
“The intent is that robust security policies, security architectures, and secure practices are established early in development and implemented throughout the lifecycle,” the guide says. “This design principle applies to both product development and Automation Solution development. When using a secure by design philosophy, security measures operate natively within the Control System or Component without requiring the addition of compensating countermeasures.”
According to the guide, reducing the attack surface is a design principle that focuses on minimizing the physical and functional interfaces of an IACS that can be accessed and exposed to potential attack. This makes it more difficult for an attack to succeed.
Another design principle is “Defense in Depth” which is defined as “the provision of multiple security protections, especially in layers, with the intent to delay or prevent an attack.” This involves implementing multiple layers of security and detection which requires attackers to break through or bypass multiple layers without being detected.
The fourth principle involves those essential functions which are required to maintain health, safety, the environment, and availability of the equipment. Essential functions include the safety instrumented function, the control function, and the ability of the operator to view and manipulate the equipment.
Standards Roadmap
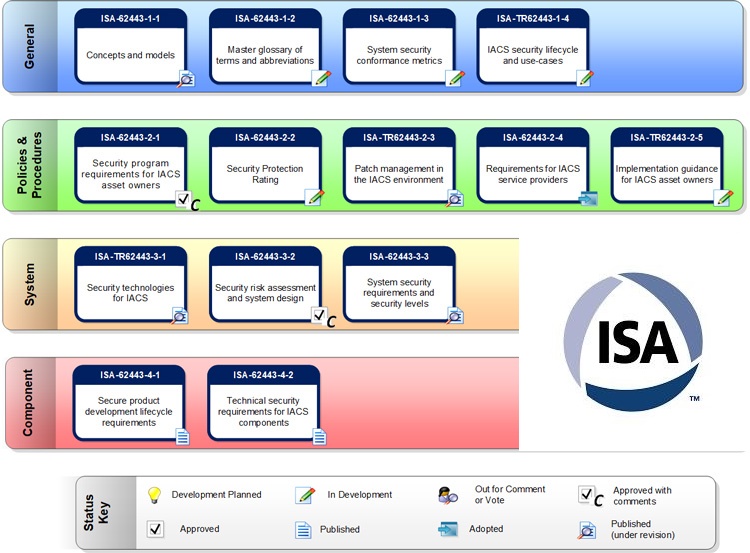
According to the guide, there are two lifecycles defined in the ISA/IEC 62443 standards. However, while most of the standards are focused on either the product development lifecycle or the automation solution lifecycle, there are also standards focused on technical requirements for systems which cover both lifecycles.
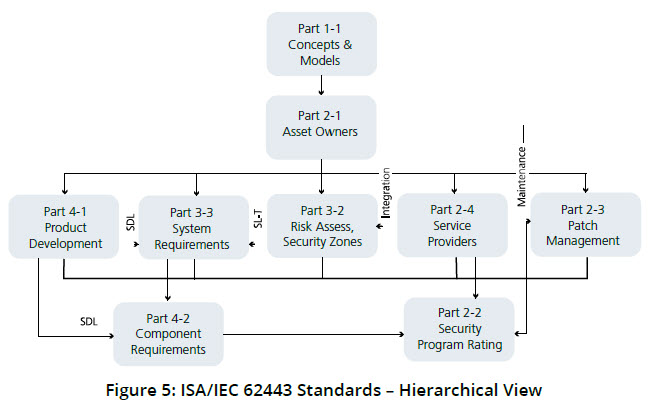 “Note that Part 3-3 spans the Product Development Lifecycle and the Integration Phase of the Automation Solution Lifecycle,” the guide says. “This is because while the Product Supplier is the main audience for Part 3-3, the Integration Service Provider may also combine Components to create Control Systems. An example would be a SCADA system, where the Integration Service Provider integrates the SCADA system with Embedded Devices (e.g., PLC) to create an Automation Solution.”
“Note that Part 3-3 spans the Product Development Lifecycle and the Integration Phase of the Automation Solution Lifecycle,” the guide says. “This is because while the Product Supplier is the main audience for Part 3-3, the Integration Service Provider may also combine Components to create Control Systems. An example would be a SCADA system, where the Integration Service Provider integrates the SCADA system with Embedded Devices (e.g., PLC) to create an Automation Solution.”
The product development lifecycle covers the process used to design, create and deliver a component for a control system product. The standards specifically for product suppliers involve establishing and sustaining a security development lifecycle, providing control system products that meet security level capabilities, providing component products that meet security level capabilities and providing ongoing lifecycle support for control system and component products.
The automation solution lifecycle defines roles for integration service providers and maintenance service providers. The first phase is an integration phase which involves product development and the second phase is the operating and maintenance phase which includes things like patch management and other processes that are used to manage the industrial control system.
Certifications and Training
The nonprofit ISA Security Compliance Institute has developed several product certification programs for control systems and components. These ISASecure programs certify that various aspects of an operation have the capability to meet the requirements of the ISA/IEC 62443 standards.
They include Security Development Lifecycle Assurance, which certifies that the security development lifecycle of a product supplier meets the requirements; System Security Assurance, which certifies that control system products have the capability to meet the requirements; and Component Security Assurance, which certifies that component products, such as embedded devices, host devices, network devices, and software applications, have the capability to meet the requirements.
ISA/IEC also offers a system of conformity assessment schemes called IECEE. These conformance assessment schemes cover a number of the IEC 62443 standards, including ISA/IEC 62443-2-4:2015/AMD1:2017, ISA/IEC 62443-3-3:2013, ISA/IEC 62443-4-1:2018, and ISA/IEC 62443-4-2:2019.
Additionally, there are a number of cybersecurity-related training courses offered by ISA. They cover topics such as using the ISA/IEC 62443 standards to secure your control system; cybersecurity for automation, control and SCADA systems; assessing the cybersecurity of new or existing IACS systems; IACS cybersecurity design and implementation, and IACS cybersecurity operation and maintenance.